Temporary email services provide disposable inboxes that shield your real identity during online activities. They are a simple, powerful tool for anyone looking to maintain privacy, prevent spam, and browse the web without leaving a permanent digital trail. By using a temporary address for sign-ups, downloads, and forum registrations, you create a crucial barrier between your personal information and the online world.
Ever felt that little pang of hesitation when a website asks for your email address? You’re not alone. In an age of data harvesting, relentless spam, and sophisticated phishing scams, our email inboxes have become frontline battlegrounds for our privacy. But what if you could simply… vanish? What if you could hand out an email address that self-destructs after its job is done, leaving no trace back to you? This isn’t spy movie fantasy—it’s the practical, accessible reality of temporary email for private browsing.
Think of it as a digital burner phone. You get a functional, real email address for a short window of time, use it to access that free e-book, sign up for a one-time discount, or register on a forum you’re casually exploring, and then let it dissolve into the ether. Your primary, personal email—the one tied to your bank, your family, and your identity—remains pristine and untouched. This simple act is a cornerstone of a smarter, more private browsing habit. In this guide, we’ll unpack everything you need to know about leveraging disposable email addresses to reclaim your online peace of mind.
Key Takeaways
- Primary Purpose: Temporary email is a privacy tool designed for short-term use, creating a barrier between your real identity and online services.
- Spam Prevention: It effectively eliminates spam and phishing attempts by sacrificing the disposable address instead of your primary inbox.
- No Registration: Most services require no sign-up, offering instant, anonymous access to a temporary inbox.
- Limited Lifespan: Emails and inboxes typically expire after a set period (e.g., 10 minutes to 24 hours), reinforcing the “use and discard” philosophy.
- Not for Critical Accounts: Never use temporary email for banking, main social media, or any account requiring long-term access and recovery.
- Complementary Tool: It works alongside other privacy tools like VPNs and browser incognito mode for a layered defense strategy.
- Legal & Ethical Use: These services are legal and ethical for protecting privacy but violate terms of service on platforms requiring verified, permanent contact information.
📑 Table of Contents
- Understanding the Disposable Inbox: What Exactly Is Temporary Email?
- The Core Benefits: Why You Should Integrate Disposable Email Into Your Routine
- Practical Guide: How to Use Temporary Email for Private Browsing (Step-by-Step)
- Limitations and Crucial Cautions: What Disposable Email Can’t Do
- Best Practices for Maximizing Privacy and Safety
- The Future of Disposable Email and the Evolving Privacy Landscape
- Conclusion: Your Digital Footprint, Your Choice
Understanding the Disposable Inbox: What Exactly Is Temporary Email?
At its core, a temporary email service (also called disposable email, throwaway email, or burner email) is a web-based platform that generates a random, functional email address for you to use instantly. The key differentiator from your Gmail or Outlook account is its intentional impermanence. These services are built with a single, clear mission: to receive emails for a limited time and then disappear.
How It Works: The Instant Inbox
You visit a site like Temp-Mail.org, Guerrilla Mail, or 10MinuteMail. The homepage immediately presents you with a randomly generated email address (e.g., [email protected]). There’s no “Sign Up” button. No password to create. No personal details to provide. That inbox is now live and waiting. You copy that address, paste it into the website you’re visiting, and any verification or welcome email it sends will appear right there on the temporary service’s page, usually refreshed automatically. After a predetermined time—often 10 minutes, 1 hour, or 24 hours—the inbox and all its messages are permanently deleted from the server. The address is then recycled and given to the next user.
The Architecture of Anonymity
These services operate on a principle of detachment. They do not require, store, or associate your IP address, browser data, or any personal identifier with the generated email address. The connection is purely between your current browsing session and their server. Once you close the tab, the link is broken. This architectural choice is what makes temporary email for private browsing so effective. It’s not about encrypting your messages (though some offer basic TLS); it’s about ensuring there is no persistent account to hack, no password to leak, and no history to subpoena.
The Core Benefits: Why You Should Integrate Disposable Email Into Your Routine
Using a temporary email isn’t about doing something shady; it’s about practicing smart digital hygiene. The benefits extend far beyond just avoiding a few spam emails.

Visual guide about Temporary Email for Private Browsing
Image source: mozilla.org
Benefit 1: The Ultimate Spam and Phishing Shield
This is the most obvious and powerful advantage. When you use your primary email to sign up for a free webinar, download a wallpaper pack, or enter a contest, you are almost certainly signing up for a marketing list. That company may sell your email to data brokers. Their database could get breached. Your inbox becomes a target. By using a disposable address, you sacrifice a throwaway resource. Any spam, phishing attempts, or data-breach notifications are sent to an address that will cease to exist in an hour. Your real inbox remains a sanctuary for important communications.
Benefit 2: Unparalleled Privacy and Anonymity
Every time you enter your email on a new site, you create a data point that can be used to profile you. It links your browsing behavior on that site to your identity. A temporary email severs that link. For users researching sensitive topics, comparing prices on travel sites without being tracked, or exploring communities they prefer to keep separate from their professional life, this anonymity is invaluable. It allows you to interact with the web without handing over a key piece of your digital identity.
Benefit 3: Bypassing “Email Gating” with Ease
The internet is full of “gated content.” Want the whitepaper? Sign up with your email. Want to read the article after 3 free pieces? Register. Want the software trial? Give us your email. Often, the content isn’t worth the permanent marketing subscription. A temporary email lets you access these resources guilt-free and without commitment. It democratizes access to information that is otherwise locked behind an email capture form.
Benefit 4: Simplifying Account Creation for Testing and Development
For developers, QA testers, or even savvy users testing a new service, creating multiple test accounts with a primary email is messy. Temporary email services allow for the rapid creation of test accounts to verify email flows, test password resets, or explore a platform’s features without cluttering a real inbox or managing multiple fake permanent accounts.
Practical Guide: How to Use Temporary Email for Private Browsing (Step-by-Step)
Integrating this tool into your workflow is remarkably simple, but knowing the best practices makes it even more effective.

Visual guide about Temporary Email for Private Browsing
Image source: gadgetgang.com
Step 1: Choosing a Reliable Service
Not all temporary email services are created equal. Look for these features:
- No Registration Required: The hallmark of a good service. You should get an inbox immediately.
- Reasonable Lifespan: 10-60 minutes is standard for quick tasks. Some offer 24-hour inboxes for projects requiring a bit more time.
- Inbox Refresh: The page should auto-refresh or have a clear manual refresh button to see new emails.
- Multiple Domain Options: Some services offer several domain names (e.g., @tempmail.demo, @disposable.com), which can help if a site blocks known disposable domains.
- Ad-Light Interface: These sites are often ad-supported. Choose one that isn’t so cluttered with misleading “Download” buttons that you risk clicking a malicious ad.
Popular, reputable options include Temp-Mail, Guerrilla Mail, and 10MinuteMail. Keep a bookmarked favorite for quick access.
Step 2: The Process: From Click to Completion
Here’s the typical flow:
- Navigate to your chosen temporary email site. Your unique inbox and address are generated instantly.
- Copy the provided email address.
- Paste it into the sign-up or contact form on the website you’re visiting.
- Complete the action (e.g., click “Sign Up,” “Get Download Link”).
- Switch back to the temporary email tab. The verification email should appear in the inbox within seconds or minutes.
- Click the link in that email (often you can do this directly from the temporary inbox) to complete the process.
- Extract what you need (the download file, the access code, the article) and then… walk away.
There is no need to log out or delete anything. The service handles the cleanup automatically when the timer expires.
Step 3: Knowing When to Use It (and When Not To)
The golden rule: Use disposable email for any interaction where you do not need a long-term, recoverable relationship with the service.
Perfect Use Cases:
- Downloading free templates, e-books, or software trials.
- Signing up for one-time discounts or coupon codes.
- Registering on a forum to read a specific thread or post a single comment.
- Accessing a news article behind an email gate.
- Testing a website’s email functionality.
- Creating a throwaway account for a casual online game.
Absolutely Avoid Use Cases:
- Primary Email for Any Service: Your main social media (Facebook, Twitter), banking, email providers, or cloud storage (Google, Apple, Microsoft). You will be locked out forever.
- Account Recovery: If you forget your password, there is no way to reset it without access to the inbox. The account is gone.
- Any Service with Legal or Financial Implications: Job applications, official government portals, subscription services you intend to keep long-term.
- Professional or Academic Submissions: Where your identity and credibility matter.
Limitations and Crucial Cautions: What Disposable Email Can’t Do
Temporary email is a powerful privacy tool, but it is not a magic shield. Understanding its limits is critical for safe and effective use.

Visual guide about Temporary Email for Private Browsing
Image source: news.mit.edu
It Is Not Encryption or a Security Suite
A common misconception is that temporary email encrypts your messages. It generally does not. The emails are stored in plain text on the service’s server. While the service itself may not log your IP, the email content is theoretically visible to the service provider. Therefore, never use a temporary email to send sensitive personal information (passwords, SSNs, credit card numbers) to anyone. Its purpose is to receive verification emails and low-risk communications, not to conduct confidential business.
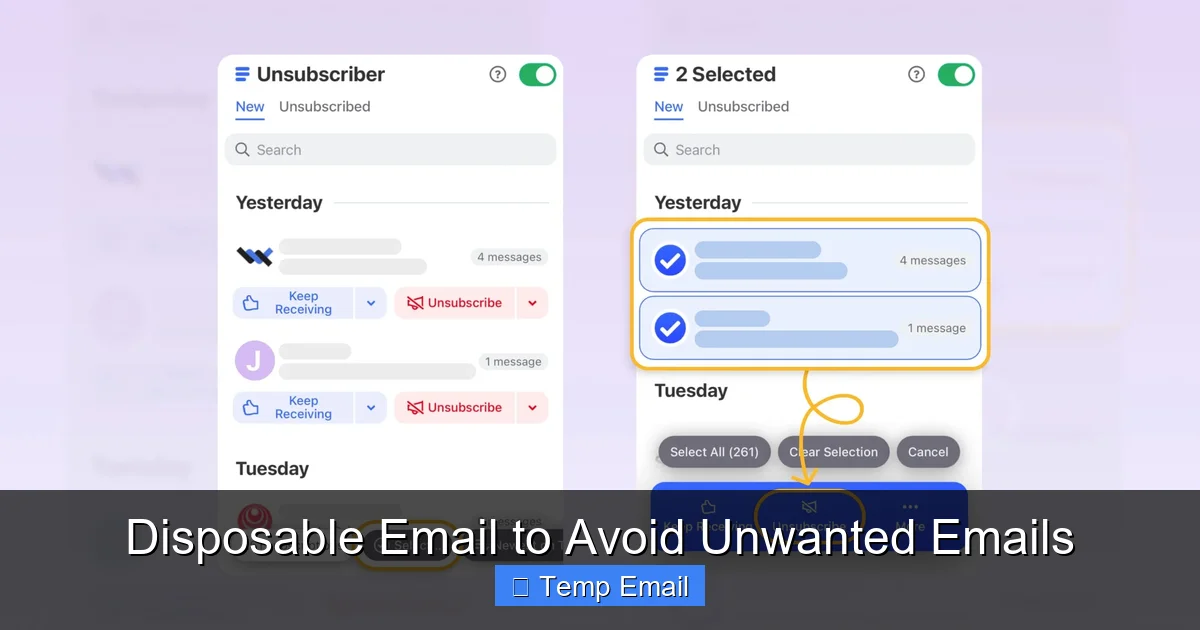
Blocklists and Detection
Many modern websites actively check email domains against known disposable email blocklists. If you try to sign up with a blocked domain, you’ll get an error message like “Please use a valid email address.” This is a cat-and-mouse game. Some services rotate domains to stay ahead of blocklists. If one service fails, trying another or a different domain from the same service might work. However, for major platforms (Google, Facebook, major banks), these blocklists are very sophisticated and nearly impenetrable.
The “Send Email” Functionality is Often Useless
Most temporary email services are receive-only. You cannot reliably send emails from these addresses. Even if a “Compose” button exists, the outgoing mail will almost certainly be flagged as spam or rejected by major providers (Gmail, Outlook, Yahoo). Do not rely on being able to send a reply from your disposable address.
No Account Persistence, No Recovery
This is the most important caution. Once the inbox expires, it is gone forever. There is no “Forgot Password” link because there is no password. There is no customer support to retrieve a missed verification email. If you need to access a service months later, you will have lost the account. This cements the rule: only use it for transactions with no future value.
Best Practices for Maximizing Privacy and Safety
To weave temporary email seamlessly and safely into your private browsing practice, follow these guidelines.
Combine with Other Privacy Tools for a Layered Approach
Temporary email is one layer. For robust privacy, use it in conjunction with:
- A Reputable VPN: This masks your IP address and encrypts your internet traffic, hiding your location from the websites you visit.
- Privacy-Focused Browsers: Browsers like Brave or Firefox with strict privacy settings and extensions like uBlock Origin and Privacy Badger prevent tracking scripts and ads.
- Browser Incognito/Private Mode: This prevents your browser from saving history, cookies, and form data from your session. Use it *with* a temporary email for a session that leaves minimal traces on your local device.
Together, these tools mean the website sees a random email from an anonymous IP via a browser that won’t save its cookies. That’s a powerful privacy combo.
Manage Your Expectations and Have a System
Don’t use a random temporary email every single time haphazardly. If you are signing up for multiple related resources from the same provider (e.g., a company offering three different whitepapers), consider using the *same* temporary email address for that specific “project” so you can receive all related emails in one place. Just remember, once you close that browser session, you may lose access if you don’t copy the needed info immediately.
Always Verify the Link Before Clicking
Even in a temporary inbox, phishing emails can arrive. The email might claim to be from “Amazon” with a link to “claim your prize.” Always hover over links (on desktop) to see the true URL before clicking. Does it go to amazon.com or amaz0n-security.com? The disposable inbox doesn’t protect you from malicious links; your own vigilance does.
Clear Your Browser After the Session
When you’re done with your private browsing session that used a temporary email, close all tabs related to the activity. Then, if you used a standard browser window (not incognito), clear your recent browsing history, cookies, and cache for those specific sites. This removes any lingering session cookies that could link your activity later.
The Future of Disposable Email and the Evolving Privacy Landscape
The demand for tools like temporary email is growing in direct response to the erosion of online privacy. As data collection becomes more pervasive, users are seeking simple, effective ways to fight back.
Rise of Integrated Privacy Features
We’re seeing mainstream platforms adopt features inspired by disposable email. Apple’s “Hide My Email” feature, part of iCloud+, automatically generates unique, forwardable email addresses that route to your real inbox. This is a corporate-sanctioned, more permanent version of the disposable concept. Similarly, Firefox Relay offers a similar service. These integrated solutions are more convenient but are tied to a paid account and ecosystem, whereas public temporary email services remain free and anonymous.
The Ongoing Arms Race
As blocklists get smarter, temporary email services evolve. We may see more services employing techniques like:
- Dynamic Domain Generation: Creating hundreds of unique domains to stay ahead of filters.
- CAPTCHA Solving Integration: Automating the process to make bulk creation harder to detect.
- API-Based Access: Allowing developers to programmatically generate and monitor addresses for app testing.
The fundamental tension will persist: websites want a real, engaged user (and their data), and privacy-conscious users want to access resources without handing over their identity.
A Cultural Shift Toward Privacy Awareness
Ultimately, the popularity of temporary email signals a positive shift. It means more users are asking, “Why do you need my email?” and “What will you do with it?” It encourages a mindset of minimal data sharing. By making the act of protecting one’s privacy as easy as a single click, these services empower everyday people to take control. The future likely holds not just better tools, but a broader expectation that privacy should be the default, not the exception you have to engineer yourself.
Conclusion: Your Digital Footprint, Your Choice
Your email address is one of the most persistent and valuable pieces of your digital identity. It’s the master key to resetting passwords, the primary channel for marketing, and a common data point in security breaches. By adopting the simple habit of using a temporary email for private browsing—for all those low-stakes, one-off interactions with the web—you perform a powerful act of self-protection. You declutter your primary inbox, you dodge countless spam campaigns, and you sever unnecessary data links that fuel the profiling economy.
This isn’t about being paranoid; it’s about being prudent. It’s the digital equivalent of using a shopping cart to carry your groceries instead of handing your wallet to the store clerk. You’re not doing anything wrong—you’re just not giving away the keys to your house for a free sample. Start today. Bookmark a reputable temporary email service. Use it the next time a blog asks for your email to read an article. Experience the quiet satisfaction of closing that tab knowing your real identity is still safely tucked away. In the battle for online privacy, the most effective weapon is often the simplest one, used consistently. Your temporary inbox is waiting.
Frequently Asked Questions
Is using a temporary email legal?
Yes, using temporary email services is completely legal in most jurisdictions. They are legitimate privacy tools. However, using them to create accounts on websites that explicitly require a “real, permanent email address” in their Terms of Service is a violation of those terms and could get your account banned.
Can a temporary email service read my emails?
Technically, yes. Since the emails are stored in plain text on their servers, the service provider could access them. This is why you should never send sensitive personal or financial information via a disposable address. Their business model relies on providing a functional service, not on reading your emails, but absolute privacy cannot be guaranteed.
What happens if I need to recover an account I made with a temporary email?
You cannot. Account recovery requires access to the inbox to receive reset links. Since the inbox and address expire, the account is permanently inaccessible. This is why the cardinal rule is to never use temporary email for any account you might need to access long-term or that holds valuable data.
Will using a temporary email affect my browsing speed or computer security?
No. A temporary email service is simply a website you visit. It does not install software on your computer. Your browsing speed is only affected by your own internet connection and the website’s performance. However, be cautious of the ads on these sites, as some may be misleading. Use an ad-blocker for safety.
Is a temporary email the same as using a VPN or incognito mode?
No, they are different tools that serve different purposes and work best together. A VPN hides your IP address and encrypts traffic. Incognito mode prevents your browser from saving local history and cookies. A temporary email protects your identity from the website you’re signing up with. Using all three simultaneously provides a much stronger layer of privacy than any single tool.
How long do temporary emails typically last?
It varies by service. Some inboxes last only 10 minutes (like 10MinuteMail), others last 1 hour, and some offer 24-hour or even 7-day retention periods. Always check the service’s policy. The lifespan is clearly displayed, so you know exactly how much time you have to retrieve any needed emails before the inbox self-destructs.